There is also a more dangerous variation of phishing, which poses a more serious threat than mass attacks. We call it spear phishing – that is, personalized phishing (spear metaphorically indicates a targeted, precise attack). It is a type of social engineering attack in which criminals do not act blindly, but already possess certain specific information about the target (victim), and intentionally use it to build trust, create a credible communication context, and manipulate the person into performing desired actions.
When criminals possess more detailed information about a potential victim – such as their first and last name, position, company name, professional relationships, recent transactions, projects, or even details from their private life – it simply becomes much easier for them to convince the victim to take an action they expect. Scammers use this data, often gathered from various sources (e.g., social media, public registers, previous data leaks, company websites), to maximize the credibility of their identity and intentions in the victim’s eyes.
Spear phishing attacks are extremely effective because the messages are precisely tailored, eliminating the typical suspicions associated with mass phishing. A criminal who inspires trust and demonstrates apparent knowledge of the context or even shows empathy will more quickly persuade us to perform a dangerous action.
We might be convinced, for example, to:
- Install malicious software: The scammer, impersonating a technical support employee or a trusted partner, can convince the victim that they are offering urgent technical support to resolve a critical problem. In reality, they are inducing the victim to install software (e.g., a fake remote desktop application) that will allow the criminal to gain remote control over the victim’s computer, steal data, or encrypt files to demand a ransom.
- Hand over confidential information: The attack can involve phishing for passwords, financial data, or key trade secrets by redirecting to a fake login page (impersonating a bank, company system, or cloud service) that looks identical to the original.
- Execute a money transfer: In a particularly dangerous variation of spear phishing, called whaling (an attack on a „big fish,” meaning management), the scammer impersonates the CEO, CFO, or another board member, urging an employee from the finance department to urgently make a confidential transfer to an account controlled by the criminals, often under the pretext of a secret transaction or urgent payment.
Spear phishing is a more advanced and harder-to-detect method because it seeks to minimize any warning signs by perfectly matching the communication to the victim’s profile. This technique is particularly regularly used in attacks on corporate and government targets.
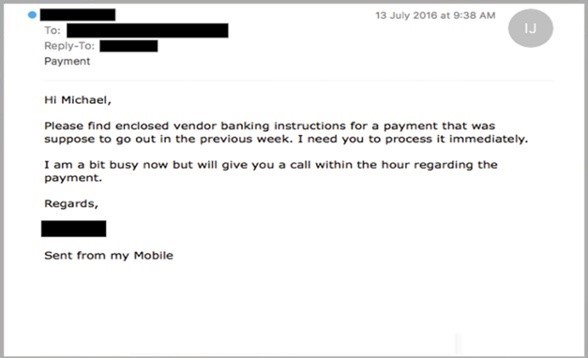
Image source: https://phishing.iu.edu/stories/
Example: Imagine Ms. Anna, who uses online banking daily. One afternoon, while checking her inbox, her attention was caught by a message titled „Urgent: Bank Account Blocked! Immediate verification required”.
The message looked very official, almost like a real message from the bank. Its graphic design, logos, and even the footer with the address and contact numbers closely resembled the authentic communications Ms. Anna was used to. What’s more, the sender field indicated the name of the bank Ms. Anna is a customer of. This created the impression that the message actually came from a trusted financial institution. The content of the message informed about an alleged unauthorized access attempt to Ms. Anna’s account and the necessity of immediately blocking it to protect funds. To „restore full functionality” and prevent permanent access blockage, Ms. Anna was asked to click on the attached link and confirm her identity and access details.
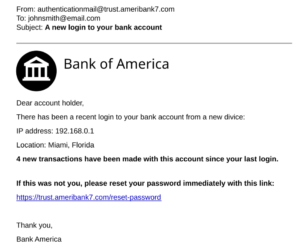
Frightened by the vision of losing access to her money and wanting to solve the problem as quickly as possible, she clicked the link and provided her details, including her login and password for online banking, on a page that was an exact copy of the bank’s website. She did not notice the subtle differences in the website address (URL) or other, less obvious warning signs. She believed she was acting according to her bank’s instructions to ensure the security of her finances. After entering the data, a message appeared on the screen about „successful verification” and a promise to restore access within a few minutes. Ms. Anna felt relieved, unaware that she had just fallen victim to a phishing attack, and her confidential data had ended up in the hands of cybercriminals. Only a few hours later, when she received an SMS notification about a large outgoing transaction, did she realize she had been deceived.